
Staying Safe, Sound, and Secure Online: Part Two - Email Security
Posted by Anonymous on Oct 07, 2015
In the last article in our Staying Safe, Sound, and Secure Online series, we explored how to stay safe when browsing online. Another common activity that hackers target is e-mail. Today we will take a look at how e-mail is being exploited, and practical things you can do to prevent evil-doers from exploiting your e-mail.
Avoid and E-mail Emergency
E-mail has become as commonplace as phones, and represent a significant part of our communication infrastructure. Because e-mail is a conduit to other technologies, it is a logical target for hackers. To provide a good defensive strategy for you, let’s first explore how attackers use e-mail. Information is gold to hackers, and there are many ways that they exploit this information. Yes, they are targeting personal information, but it goes so much deeper than that. Not only are they targeting personal information, but they are using people to step up their attacks on organizations, using e-mail to mine information that will allow them to stage cyber-attacks.
Anatomy of Cyber Attacks
We will discuss cyber-attacks as a whole in a later article, but it is important to understand that threat actors (hackers, cyber criminals) use e-mail as one of the methods in multi-prong cyber-attacks. We’ll take a look at two of these methods and how you can avoid falling into their trap.
Phishing
You may already be familiar with the term “phishing”. Simply put, phishing is a method where hackers send out a legitimate-looking e-mail with the intent of luring the user into an action. The better phishing schemes utilize company logos and clean, nicely formatted HTML e-mail templates. They usually contain some kind of link or call to action. Here’s an example of a phishing e-mail:
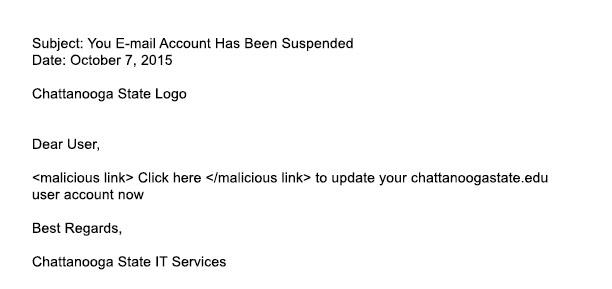
Phishing Example
As you can see, we have formatted this e-mail pretty plainly for purposes of this article (no need to make it easier for an attacker). In this case, the call to action is for you to click on a link. This link would take you to a website (probably cleverly formatted to look like a familiar site), and would ask you for either information such as a password, credit card, or other personal information, or it might download malware or viruses to your computer.
So how, can an attacker user this to escalate their intrusion into a system? If you had happened to provide your campus credentials in this phishing scheme, you would give an attacker access into your campus systems. An attacker could then use these elevated privileges to begin another attack. If they downloaded malware or a virus, it could be used to gain access to your campus systems or even some of your personal accounts.
Spear phishing
Spear phishing is phishing evolved. Hackers first gather as much information about an organization as possible, including events and activities going on with the organization, as well as legitimate e-mail addresses. After gleaning this information, attackers craft a highly targeted e-mail that appears that it is from a legitimate contact. Here’s an example:
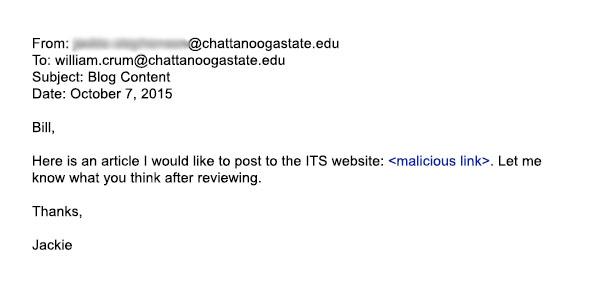
Spear Phishing Example
Again, the purpose of this attack is to trick you into opening the e-mail or clicking a link. In this case, attackers have targeted the user by (hopefully, from their point of view) making the e-mail appear to be from someone inside of their organization.
Protecting yourself, and the campus
In many ways you, as the employee, are our best, first line of defense against cyber-attacks. Our job, as the IT Services department, is to give you the weapons to help defend our campus. So, how can you get in the fight?
- If something feels “phishy,” it probably is. Take the cautious approach and delete the item. You can report suspicious e-mails at [email protected].
- Beware of e-mail that has a generic salutation such as “Dear faculty member.”
- Beware of e-mail with an urgent call to action. Unless you are aware of a work-related project with an urgent need, don’t open or click on links in the e-mail.
- For suspicious e-mail that appears to be from a colleague, you may be targeted in a spear phishing attack.
- Only click links in an e-mail that you are certain are from a trusted source. If you’re not sure, it is better to leave it alone and report the suspicious e-mail to [email protected].
Nothing is foolproof. Attackers keep getting more and more sophisticated in their activities. Staying knowledgeable and keeping vigilant is the only real defense we have against e-mail attacks. We will do our best to keep you informed on emerging threats and give you the information to arm yourselves in order to keep up the good fight.
Here’s an interesting link to test your Phishing IQ (don’t worry, this is a legitimate link): http://www.sonicwall.com/furl/phishing.
In our next installment, we will look at viruses and malware and what you can do to keep yourself (and the campus) protected.






